Contents
Docs
General
- Introduction
- Android versions matrix
- What is Android Enterprise?
- Android Enterprise feature requests
- Considerations when migrating from device administrator to Android Enterprise
- Upgrading your Android Enterprise binding to a managed Google domain
- What is Android Enterprise Recommended?
- Android Enterprise FAQ
- How to migrate Android devices from one EMM to another
- Android Enterprise device testing
- What is Private Space in Android 15, and how can organisations manage it?
- Why don't all Android devices come with GMS?
- What is Android One?
- What are managed configurations?
- Android Enterprise vs Device Admin: Why DA is no longer suitable
- Considerations for choosing Android in the Enterprise
- Feature spotlight: Android Smartlock
- Android glossary
- Android version evolution graphics
- Infobyte: Device Admin deprecation
- How to submit a device for Android Enterprise Recommended validation
- How to view software version information
- How to capture a bug report and device logs
- Gartner comparison of security controls for mobile devices 2019
Provisioning
- How to become a zero-touch enrolment reseller
- Android Enterprise provisioning methods
- What is Android zero-touch enrolment?
- Android Enterprise zero-touch console administration guide
- Android Enterprise DPC identifier collection
- Android Enterprise provisioning guides
- Android Enterprise zero-touch DPC extras collection
- Infobyte: Android Enterprise deployment scenarios
- Infobyte: Android Enterprise fully managed provisioning methods
- Manual Android Enterprise work-managed QR code generation for MobileIron
Work profile
Fully managed
App management
- Set up Hypergate's Kerberos Authentication on MobileIron Core for Android Enterprise
- Managed Google Play, allowlist or blocklist?
- Considerations when deploying MTD with Android Enterprise
- Why you shouldn't install apps from unknown sources
- What is OEMConfig?
- Create and manage private apps for Android Enterprise
- Create and manage web apps for Android Enterprise
- Using Google Play application tracks with EMM
- How to locate a private Android app assigned to an organisation ID
- How to host enterprise apps outside of Google Play
- The Google Play iFrame app approval flow is deprecated
- Android 13 adds notifications access as a runtime permission
- Android 13 & up restricts permissions when apps are sideloaded
- Android 14 blocks apps targeting old Android versions
- Android minimum target SDK matrix
- Android system app database
- How to resolve common Android app install failures, by error message
FAQ
- Is Android Enterprise supported on uncertified (non-GMS) devices?
- Can apps be sideloaded into the Private Space?
- Is Private Space supported on fully managed devices?
- Why don't Private Space apps go through VPN?
- How can apps be managed in the Private Space?
- Are Private Space apps visible to enterprise admins?
- Are Private Space applications truly hidden?
- Does Samsung support Android Enterprise?
- Is it possible to manage personal applications on a work profile device?
- Why has USB data access been disabled suddenly?
- What versions of Android support Android Enterprise?
- How to check if an Android device is GMS/Play Protect certified?
- Is it possible to manage eSIM?
- Can I manage APNs through AMAPI?
- Why is my organisation name showing on managed devices?
- Can I route specific apps through 5G network slicing?
- To use Android Enterprise do I need to buy Google Workspace (G Suite) and register my domain?
- What is a managed Google domain, and should I upgrade?
- Is Android Enterprise supported on XR headsets?
- What devices should I buy for my organisation?
- What is the difference between GMS and EDLA certification for enterprise?
- How do Samsung Knox and Android Enterprise policies interact?
- If Android Enterprise is supported from Lollipop, why is Marshmallow often mentioned instead?
- What’s the difference between Device Admin and Android Enterprise?
- What is the Android Enterprise bind?
- Can I change the account I used to bind Android Enterprise?
- Is it possible to bind Android Enterprise with multiple EMMs using one account?
- How do I remove the Android Enterprise bind from my current EMM?
- How do I choose an EMM for Android Enterprise?
- What network requirements does Android Enterprise have?
- What is Android Enterprise Recommended?
- My AER device doesn’t work properly with Android Enterprise, what should I do?
- What is Advanced Protection, and can it be managed?
- Is Android One better than AER? (Or the other way around?)
- How do I configure Google Workspace domains for provisioning?
- What’s the best provisioning method?
- What’s the difference between allow adding accounts vs allow configure credentials?
- Is it possible to utilise a single VPN connection across the entire device?
- Is it possible to utilise multiple VPN connections within a profile?
- Does Android support Kerberos natively?
- What’s the difference between device based accounts and user based accounts?
- How do I manage the new notifications runtime permission in Android 13?
- Can organisations see applications outside of the work profile?
- What can my employer see on my personal device with a work profile?
- What happens to my data when the work profile is removed?
- What is the difference between MAM and work profiles for BYOD?
- Can organisations deploy applications to the parent profile in a work profile deployment?
- Why does the work profile drain my battery?
- Why are my work profile notifications delayed or missing?
- Is it possible to migrate from DA to AE work profile without a re-enrol?
- Can I turn off my work profile?
- What is a work challenge?
- Enrolment failed but the work profile was created. How do I remove it?
- Why can’t I install or uninstall apps on my managed device?
- How can I provision a fully managed device?
- Is it possible to “retire” (or enterprise wipe) a fully managed device?
- Devices factory reset as soon as they’re enrolled, why?
- Is Factory Reset Protection enabled on fully managed devices?
- What is the difference between FRP and Enterprise FRP?
- Is it possible to migrate fully managed devices between EMM solutions?
- How has COPE changed in Android 11?
- Does Intune support COPE?
- Can organisations see applications outside of the work profile on a COPE device?
- Does Android Enterprise support WearOS?
- Can organisations deploy applications to the parent profile in a COPE deployment?
- Is it possible to migrate from fully managed to COPE without a factory reset?
- How should system applications be handled on a COPE device?
- What OEMs currently support zero-touch?
- Where are zero-touch resellers located?
- Does zero-touch cost anything?
- Does Android Auto work on fully managed devices?
- Is an EMM still required with zero-touch?
- What is the content protection policy in AMAPI?
- What happens if a fully set up device is added to the zero-touch console?
- What happens if a user starts setting up a device before the zero-touch config is applied?
- What happens if a zero-touch config is removed from an enrolled device?
- My AMAPI project returns a usage limit error, why?
- Can I add/remove users on a fully managed device?
- What happens if a new config for a different EMM or server is applied to an enrolled device?
- How can I access a Wi-Fi captive portal when devices are in Kiosk?
- What happens if a zero-touch assigned device is reset?
- What is Device Trust from Android Enterprise?
- Why does zero-touch or KME not trigger after a factory reset on Android 15+?
- What happens if a device is unregistered from the zero-touch console?
- What enterprise features are new in Android 16?
- What is Identity Check on Android?
- Can a device be OTA managed from the zero-touch console?
- What happens when a managed device receives a major Android update?
- Can I migrate devices from a custom DPC to AMAPI?
- Avoiding configuration issues in Google Workspace with GEM & 3rd party EMM
- What is the difference between AMAPI and a custom DPC?
- Does enrolling via zero-touch slow down or cause any delay to the setup process while it’s retrieving the zero-touch config?
- What happens if my Android Enterprise bind account is disabled or deleted?
- What is the AMAPI MCP server?
- Can I manage Private DNS settings through AMAPI?
- What deployment scenario will a zero-touch device enrol under?
- Why does zero-touch require so much touching?
- Can I set Device Owner without a factory reset?
- Can anyone add a device to the zero-touch console?
- Is it possible for an organisation to add previously-purchased devices to zero-touch?
- Can a MADA device be converted to EDLA?
- Can anyone remove a device from the zero-touch console?
- Does Samsung support zero-touch?
- Is it possible to set a zero-touch default configuration?
- Is it possible to bulk update zero-touch devices?
- Is it possible to change zero-touch resellers?
- Are all zero-touch devices Android Enterprise Recommended?
- What are DPC extras?
- What should I put in DPC extras?
- How do I set up zero-touch enrollment when my device reseller is not a zero-touch partner?
- What happens if a device is uploaded to zero-touch with the wrong manufacturer?
- The device registered with zero-touch, but doesn’t launch during setup, why?
- Does Android Go support zero-touch?
- Why are my zero-touch devices randomly factory resetting?
- Are employee-owned devices eligible for zero-touch?
- How do I turn off Google Play app collections?
- What’s the recommended way of managing private (in-house) applications?
- Is it possible to deploy app shortcuts to the homescreen of an Android Enterprise device?
- What are AMAPI application roles?
- Is it possible to backup & restore device data on a fully managed device?
- What is Lost Mode on Android Enterprise?
- The Google Play iFrame is missing a feature in my UEM. How do I enable it?
- How do I configure allowlist/blocklist domains for Google Chrome?
- Does Picture-in-Picture work in kiosk (lock task) mode?
- How to configure Chrome managed bookmarks
- Why does Samsung Smart Switch not work on fully managed devices?
- Play Protect blocked my DPC, why?
- Can Google Play Protect remove apps from managed devices without admin approval?
- What is enhanced fraud protection, and can it block enterprise apps?
- Has Play Protect changed how it handles sideloaded apps on managed devices?
- What is Google Play developer verification, and how does it affect enterprise?
- Does AMAPI support direct APK installation?
- Why can't I find apps in managed Google Play after approving them?
- Are Google Play System Updates managed by Android Enterprise system update policies?
- What enterprise features are new in Android 15?
- Can I purchase paid apps through managed Google Play?
- Can I control default applications through AMAPI?
- Why is my kiosk app UI broken after updating to Android 15?
- Why are managed Google Play apps stuck on pending?
- Why is work profile enrolment failing?
- Why don't managed configurations work with app tracks?
- How do I prevent users from escaping kiosk (lock task) mode?
- How do I manage credential providers and passkeys on managed devices?
- How does conditional access work with Android Enterprise?
- How does cross-profile data sharing work in a work profile?
- What are the AMAPI device quota limits?
- What is the key attestation root certificate change in 2026?
- Can I rename my managed Google Play organisation?
- How do I manage generative AI apps and features on managed devices?
Change log
Considerations for choosing Android in the Enterprise
Contents
The below document covers off a number of both Android and Android Enterprise features, so some understanding of Android Enterprise is required. To learn more about Android Enterprise, click here.
Android is secure
#The perception of Android security being subpar has long been proven incorrect. From Google’s pivot to enterprise in Android 5.0 Lollipop to today, security has been a key focus of every release.
Not convinced?
Google publishes an annual Android Security Paper detailing platform protections in depth. The 2026 edition highlights the shift from malware-centric defence to behavioural protection, OS-level scam intervention, and hypervisor-based isolation via pKVM - all of which benefit enterprise deployments significantly.
For a historical comparison, Gartner ranked Android higher than iOS in a number of areas between 2016 and 2019, including kernel security, exploit protection, network security, and workspace isolation - the results of which can be found in this report (12/2017) and this report (2019) should you have a Gartner subscription, if not here’s an overview:
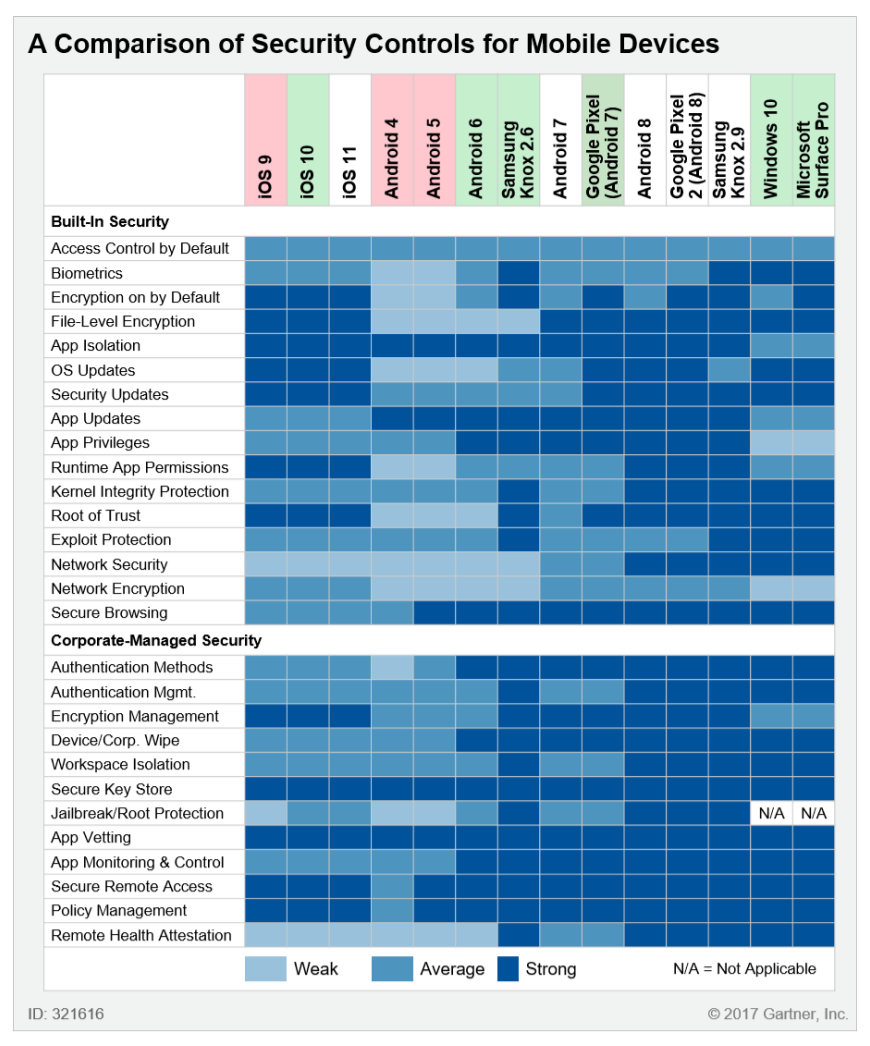 Source: Gartner, December 2017. Thanks to Samsung for making this available on the public internet!
Source: Gartner, December 2017. Thanks to Samsung for making this available on the public internet!
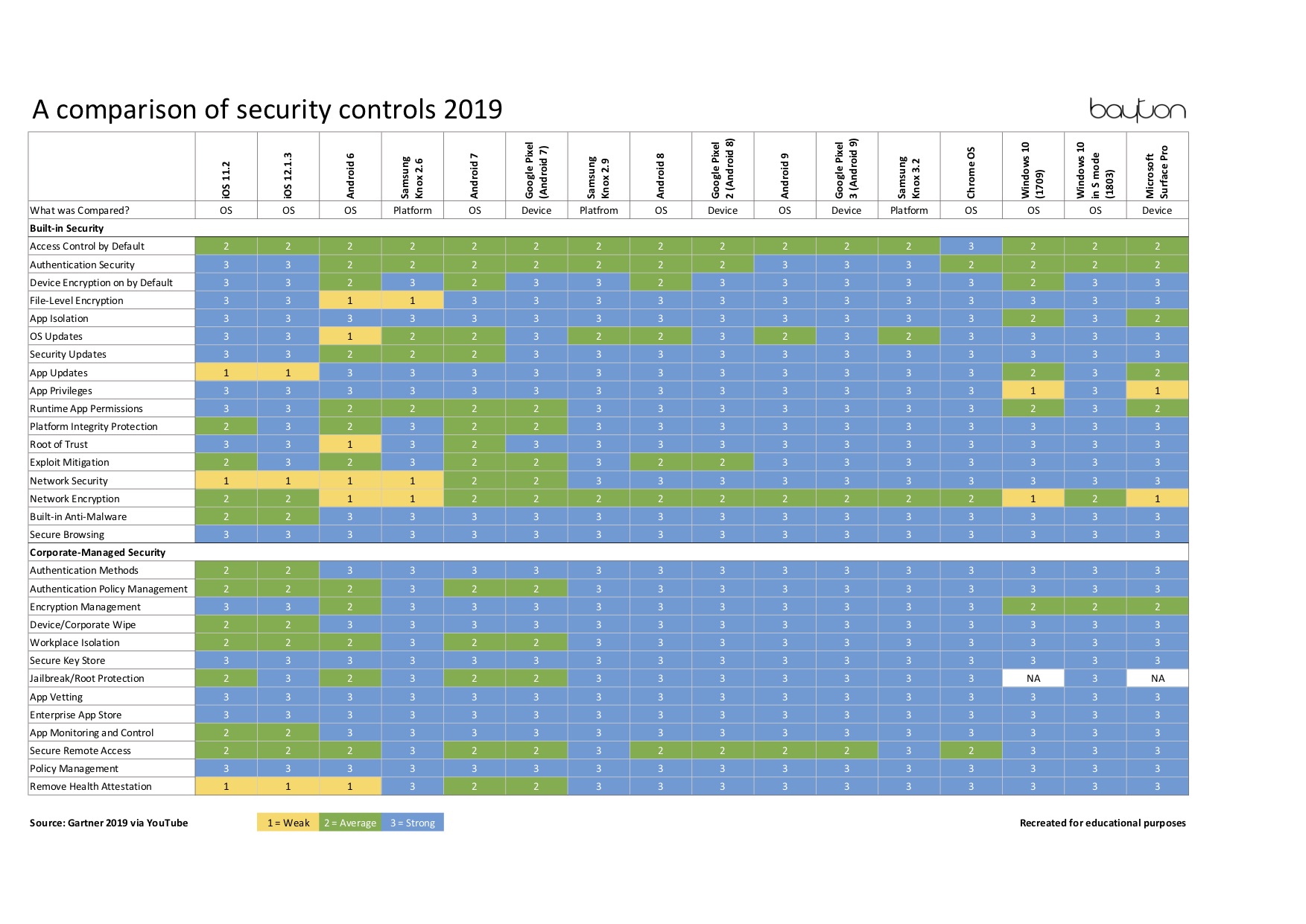 Source: Gartner, January 2019. Adapted from this source.
Source: Gartner, January 2019. Adapted from this source.
Let’s dive a little deeper into Android security:
Corporate/personal data separation
#The two deployment scenarios that make use of the work profile are the aptly named work profile (BYOD) and work profiles on fully managed device (COPE), the latter replaced by work profiles on company owned devices in Android 11. In both BYOD and the two COPE scenarios, work data is securely isolated and separately encrypted on disk.
iOS may have app sandboxing, but so does Android with each application running as it’s own user ID (UID), with the added benefit of profile isolation providing a separate user space from the parent profile as well! Applications within each profile by default cannot communicate with one another, offering far greater work/personal application isolation than app sandboxing alone.
Architecture component isolation
#Android is built up of six major components:
- Applications
- Android framework
- Native libraries
- Android runtime
- Hardware Abstraction Layer (HAL)
- Kernel
Each of these components are isolated, running in their own domains, meaning should any vulnerability be exploited in one component, it will not grant access to the others by default.
Combined with such capabilities as verified boot, downgrade protection and more, devices are constantly monitored for unauthorised changes and will prevent a boot accordingly, ensuring the device remains secure.
Monthly security patches
#Android benefits from a monthly security patch cycle to maintain high levels of security against exploits and vulnerabilities discovered in the wild.
With approximately 3.9 billion active Android devices globally, security patches reach an enormous number of devices every month. Devices in the Android Enterprise Recommended programme are mandated to push these updates within 90 days of Google’s release, and many OEMs now commit to five or more years of security updates for their flagship and enterprise devices.
Project mainline (Google Play System Updates)
#Since Android 10, Google has been migrating core Android OS components into independently updatable mainline modules. These take aspects of the OS that have previously only been updatable through an OEM-distributed OTA update (as and when that OEM felt like doing one) and allow them to be updated additionally through Google Play, mostly in the background like many other applications.
In Android 10 the number of modules sat at 12, growing to 30 in Android 13 and 37 in Android 14, covering connectivity, multimedia, and core framework components. The count continues to grow with each release.
In addition to monthly security updates (SPLs, security patch level, delivered as SMRs, security maintenance releases), Google Play System Updates can be distributed as and when required to tackle component-level security issues or bug fixes. This dramatically improves time to resolution for issues in comparison to other OS platforms.
Play Protect
#Google’s Play Protect suite of solutions includes the world’s largest mobile threat detection service, scanning over 340 billion apps daily across approximately 2.8 billion devices. In 2025 alone, Play Protect identified more than 27 million new malicious apps from outside Google Play and prevented 1.75 million policy-violating apps from being published on the store.
Play Protect is always-on, and will take action on any known potentially harmful application (PHA) found on a device, as well as any known bad websites via the Safe Browsing service to proactively warn users of danger. Real-time on-device scanning now leverages AI to detect behavioural anomalies even in apps installed from outside the Play Store.
Play Protect of course isn’t infallible, and I’d support organisations who augment Play Protect’s capabilities with an MTD solution, however it’s an ever-improving service utilising machine learning to evolve over time, and does a pretty good job for most use cases. Combined with options to prevent installation of applications from unknown sources, USB debugging and more, a corporate device can safely and successfully avoid PHAs.
Open source
#Android’s open source nature allows anyone, anywhere to access the code that makes up the Android operating system.
Vulnerabilities and bugs therefore aren’t dependent on Google for discovery, but can be found by anyone who takes the time to dive into the repositories; the source remains under constant scrutiny by the wider community which leads to a stronger OS.
Android is evolving
#Some years ago recommending an Android device in the enterprise may have raised an eyebrow. Prior to Android 5.0 security was not perceived to be a priority and management (outside of Samsung at least) was hardly reliable.
A lot has changed since then.
GMS certified devices since Android 6.0 are mandated to support the Android Enterprise solution sets, guaranteeing a reliable, consistent user experience across OEMs.
The days of bringing devices on board and hoping the exchange profile applies successfully are very much over.
Even today things are improving still, with the introduction of OEMConfig OEMs can extend on the base set of Android Enterprise APIs in order to deliver bespoke management capabilities in a way that’s faster and more reliable than ever before. OEMConfig offers zero-day support for new features and capabilities without EMM vendors having to lift a finger.
OEMs such as Samsung and Zebra have >1000 APIs available in addition to fundamental Android Enterprise capabilities for incredibly granular management. Through OEMConfig, these APIs can be (and are for Zebra) exposed for simple, zero-day support of every new feature published. More and more OEMs will build out their unique management capabilities as OEMConfig evolves.
Check out the linked article to understand how OEMConfig will transform Android management.
Android is flexible
#Organisations demand flexibility; in process, use-case, form factor and budget. Android is the most versatile mobile OS on the planet.
Management scenarios
#Considering BYOD? Dedicated? Something in between? With four individual solution sets to choose from, Android offers a management scenario to suit all applications.
From: What is Android Enterprise and why is it used?
The in-depth document What is Android Enterprise and why is it used? outlines these deployment scenarios and their applications, while this infographic offers a deep-dive on each deployment scenario specifically.
Whether your organisation wants to permit personal devices whilst managing corporate data on a secure, isolated, separately encrypted profile, or desires full control over the device, Android Enterprise offers all of this in a way that is quick and simple to manage.
Provisioning methods
#Perhaps devices are primarily located in a warehouse or other close-proximity situation where it makes sense to utilise a master device to provision devices with a bump, or perhaps devices are shipped directly to end users and should be set to provision over the air. Android can accommodate these scenarios and more.
There are a number of provisioning methods available for Android devices, including:
- NFC bump
- QR code scan
- DPC identifier
- Zero-touch enrolment
- Knox Mobile Enrolment (KME)
- Other OEM-specific provisioning methods
As above, an NFC bump makes sense where many devices are located in close proximity, while QR code and DPC identifier offer a means for remote provisioning in ways that are easy to understand.
For devices to be ready to provision straight from the box, zero-touch enrolment provides the ability to pre-configure devices before the box is even opened, and is supported on all GMS-certified devices running Android 8.0 and above.
For Samsung devices, Knox Mobile Enrolment (KME) offers the same capability and is deeply integrated with the Knox ecosystem.
More information on provisioning methods can be found in the provisioning methods guide and this handy infographic.
Form factor
#Are phones and tablets too.. consumer? Does your organisation rely on fixed endpoints, smartphone systems, bespoke logistics or warehouse scanners, specialised interactive displays, or something else?
Not only has Android shipped on phones, tablets and foldables in all shapes and sizes, Android can be equally found on rugged devices, smart displays, point-of-sale endpoints, XR headsets, vehicles, projectors, and many other specialised hardware types.
If a form factor doesn’t exist that suits an organisation's needs, one can be developed with any number of specialist hardware manufacturers.
No matter the application, there is – or can be – a form factor to suit. Android isn’t limited to only phones and tablets in a couple of sizes.
Budget
#Like Android’s flexibility in form factor, the same is true for budget.
While Apple continues to inflate the prices of their product lines to numbers which far exceed the budgets of many organisations (to their detriment), an Android Enterprise Recommended, GMS certified and enterprise-suitable device can be picked up at a fraction of the cost, cheaper still with carrier-arranged hardware funds.
Organisations can of course opt for flagship handsets and pay the premiums associated with these feature-rich devices, however there’s no obligation to do so.
Those purchased on the mid-range scale benefit equally from security patches, OS upgrades, excellent battery life and more. These days budget doesn’t mean poor quality.
Android is simple to manage
#Taking Gartner’s research into consideration, highlighting Android’s clear lead in security controls over iOS, here are some examples of how Android excels in simplicity of management:
Managed Google Play
#A corporate version of Google Play permitting only applications approved by administrators; the primary Play Store on fully managed devices, or the badged Play Store for work profile-enabled devices.
Managed Google Play offers complete control over the applications permitted on a managed device without affecting the native look and feel of the device.
In conjunction with managed Google or Google Play accounts, applications can be distributed silently and simply, updated automatically, restricted from uninstallation and more.
Add in the ability to create, manage and deploy in-house applications with only a few clicks, and a similar process for deploying web applications for direct access to corporate sites and resources, and managed Google Play becomes a one-stop solution for all forms of quick, simple application management.
What’s more, organisations can take application distribution a step further with managed configurations; inputting within the EMM the relevant details, these applications can be preconfigured on installation, meaning far less work for end-users setting up their devices.
System and application updates
#System update control is critical in enterprise, administrators need the control to be able to force updates on devices, postpone updates, and schedule them for outside of working hours.
Application update control may be just as important, whether to update immediately, over Wi-Fi only, not at all or during a scheduled time slot.
Android does all of this, providing complete, granular control over when and how updates occur for managed devices to ensure devices remain secure, or to offer a little extra time for testing before initiating a corporate roll-out. Samsung’s Knox E-FOTA service takes this a step further, offering the ability to target a particular OS version until such time later versions have been validated by the business.
Android supports work/life balance
#It’s not all about how a device is managed during business hours, employees may be glued to their devices 7 days a week! Providing tools to promote a stronger work/life balance by encouraging downtime and trust amongst employees is crucial to ensure a happy, healthy and productive workforce. Here’s how Android can help:
Turning off the work profile
#Downtime is an important aspect of modern life. Being always-on, always connected can be detrimental to employee health and well-being, so providing tools to quickly and easy fully disconnect from work is an incredibly important feature, one which puts end-users in control as much as administrators.
The work profile can be turned off with a simple toggle of the quicksettings tile, or within the app drawer (OEM launcher support required) at any time, and from Android 11 can even be scheduled through Digital Wellbeing. All corporate applications will temporarily disable and no notifications, sync or any other related activities will be performed until the profile is turned back on.
For countries with laws around the right to disconnect, EMM policies can automate this functionality as required, where supported, and from Android 11 can also set policies depicting the maximum amount of time the work profile can be disabled to ensure employees can't abuse this feature.
Promoting privacy
#Another key benefit of the work profile over legacy, full-device management for BYOD deployments is privacy.
When an Android device is enrolled into a BYOD programme, the organisation creates a dedicated work profile on the device in which corporate applications and data reside; there is little device-level management the organisation can enforce, but more importantly, there is almost nothing an organisation can see in the parent profile (device) from a personal data point of view.
The apps users install, the data users generate, it is all completely invisible to the EMM solution managing the work profile, as the EMM agent (or DPC) sits within the isolated work profile it creates and not within the parent profile – or device-wide as it would be on other platforms.
For end-users, hoping the organisation is opting not to sync personal data up to the EMM console is not good enough. Choose a platform that doesn’t permit this to begin with: Android.
Check out what can employers see on work profile devices? for more on this topic.
As Android 11 relies on the work profile deployment scenario for enabling its work profiles on company owned devices deployment scenario, all of the above equally applies to COPE deployments on anything running Android 11 or later.
Conclusion
#With the above in mind, hopefully the case for Android in the enterprise has been adequately made, but this is only scratching the surface. For more details on Android Enterprise, the modern management solution for Android devices, check out the vast selection of documents, guides and articles located here: Android.
Docs
General
- Introduction
- Android versions matrix
- What is Android Enterprise?
- Android Enterprise feature requests
- Considerations when migrating from device administrator to Android Enterprise
- Upgrading your Android Enterprise binding to a managed Google domain
- What is Android Enterprise Recommended?
- Android Enterprise FAQ
- How to migrate Android devices from one EMM to another
- Android Enterprise device testing
- What is Private Space in Android 15, and how can organisations manage it?
- Why don't all Android devices come with GMS?
- What is Android One?
- What are managed configurations?
- Android Enterprise vs Device Admin: Why DA is no longer suitable
- Considerations for choosing Android in the Enterprise
- Feature spotlight: Android Smartlock
- Android glossary
- Android version evolution graphics
- Infobyte: Device Admin deprecation
- How to submit a device for Android Enterprise Recommended validation
- How to view software version information
- How to capture a bug report and device logs
- Gartner comparison of security controls for mobile devices 2019
Provisioning
- How to become a zero-touch enrolment reseller
- Android Enterprise provisioning methods
- What is Android zero-touch enrolment?
- Android Enterprise zero-touch console administration guide
- Android Enterprise DPC identifier collection
- Android Enterprise provisioning guides
- Android Enterprise zero-touch DPC extras collection
- Infobyte: Android Enterprise deployment scenarios
- Infobyte: Android Enterprise fully managed provisioning methods
- Manual Android Enterprise work-managed QR code generation for MobileIron
Work profile
Fully managed
App management
- Set up Hypergate's Kerberos Authentication on MobileIron Core for Android Enterprise
- Managed Google Play, allowlist or blocklist?
- Considerations when deploying MTD with Android Enterprise
- Why you shouldn't install apps from unknown sources
- What is OEMConfig?
- Create and manage private apps for Android Enterprise
- Create and manage web apps for Android Enterprise
- Using Google Play application tracks with EMM
- How to locate a private Android app assigned to an organisation ID
- How to host enterprise apps outside of Google Play
- The Google Play iFrame app approval flow is deprecated
- Android 13 adds notifications access as a runtime permission
- Android 13 & up restricts permissions when apps are sideloaded
- Android 14 blocks apps targeting old Android versions
- Android minimum target SDK matrix
- Android system app database
- How to resolve common Android app install failures, by error message
FAQ
- Is Android Enterprise supported on uncertified (non-GMS) devices?
- Can apps be sideloaded into the Private Space?
- Is Private Space supported on fully managed devices?
- Why don't Private Space apps go through VPN?
- How can apps be managed in the Private Space?
- Are Private Space apps visible to enterprise admins?
- Are Private Space applications truly hidden?
- Does Samsung support Android Enterprise?
- Is it possible to manage personal applications on a work profile device?
- Why has USB data access been disabled suddenly?
- What versions of Android support Android Enterprise?
- How to check if an Android device is GMS/Play Protect certified?
- Is it possible to manage eSIM?
- Can I manage APNs through AMAPI?
- Why is my organisation name showing on managed devices?
- Can I route specific apps through 5G network slicing?
- To use Android Enterprise do I need to buy Google Workspace (G Suite) and register my domain?
- What is a managed Google domain, and should I upgrade?
- Is Android Enterprise supported on XR headsets?
- What devices should I buy for my organisation?
- What is the difference between GMS and EDLA certification for enterprise?
- How do Samsung Knox and Android Enterprise policies interact?
- If Android Enterprise is supported from Lollipop, why is Marshmallow often mentioned instead?
- What’s the difference between Device Admin and Android Enterprise?
- What is the Android Enterprise bind?
- Can I change the account I used to bind Android Enterprise?
- Is it possible to bind Android Enterprise with multiple EMMs using one account?
- How do I remove the Android Enterprise bind from my current EMM?
- How do I choose an EMM for Android Enterprise?
- What network requirements does Android Enterprise have?
- What is Android Enterprise Recommended?
- My AER device doesn’t work properly with Android Enterprise, what should I do?
- What is Advanced Protection, and can it be managed?
- Is Android One better than AER? (Or the other way around?)
- How do I configure Google Workspace domains for provisioning?
- What’s the best provisioning method?
- What’s the difference between allow adding accounts vs allow configure credentials?
- Is it possible to utilise a single VPN connection across the entire device?
- Is it possible to utilise multiple VPN connections within a profile?
- Does Android support Kerberos natively?
- What’s the difference between device based accounts and user based accounts?
- How do I manage the new notifications runtime permission in Android 13?
- Can organisations see applications outside of the work profile?
- What can my employer see on my personal device with a work profile?
- What happens to my data when the work profile is removed?
- What is the difference between MAM and work profiles for BYOD?
- Can organisations deploy applications to the parent profile in a work profile deployment?
- Why does the work profile drain my battery?
- Why are my work profile notifications delayed or missing?
- Is it possible to migrate from DA to AE work profile without a re-enrol?
- Can I turn off my work profile?
- What is a work challenge?
- Enrolment failed but the work profile was created. How do I remove it?
- Why can’t I install or uninstall apps on my managed device?
- How can I provision a fully managed device?
- Is it possible to “retire” (or enterprise wipe) a fully managed device?
- Devices factory reset as soon as they’re enrolled, why?
- Is Factory Reset Protection enabled on fully managed devices?
- What is the difference between FRP and Enterprise FRP?
- Is it possible to migrate fully managed devices between EMM solutions?
- How has COPE changed in Android 11?
- Does Intune support COPE?
- Can organisations see applications outside of the work profile on a COPE device?
- Does Android Enterprise support WearOS?
- Can organisations deploy applications to the parent profile in a COPE deployment?
- Is it possible to migrate from fully managed to COPE without a factory reset?
- How should system applications be handled on a COPE device?
- What OEMs currently support zero-touch?
- Where are zero-touch resellers located?
- Does zero-touch cost anything?
- Does Android Auto work on fully managed devices?
- Is an EMM still required with zero-touch?
- What is the content protection policy in AMAPI?
- What happens if a fully set up device is added to the zero-touch console?
- What happens if a user starts setting up a device before the zero-touch config is applied?
- What happens if a zero-touch config is removed from an enrolled device?
- My AMAPI project returns a usage limit error, why?
- Can I add/remove users on a fully managed device?
- What happens if a new config for a different EMM or server is applied to an enrolled device?
- How can I access a Wi-Fi captive portal when devices are in Kiosk?
- What happens if a zero-touch assigned device is reset?
- What is Device Trust from Android Enterprise?
- Why does zero-touch or KME not trigger after a factory reset on Android 15+?
- What happens if a device is unregistered from the zero-touch console?
- What enterprise features are new in Android 16?
- What is Identity Check on Android?
- Can a device be OTA managed from the zero-touch console?
- What happens when a managed device receives a major Android update?
- Can I migrate devices from a custom DPC to AMAPI?
- Avoiding configuration issues in Google Workspace with GEM & 3rd party EMM
- What is the difference between AMAPI and a custom DPC?
- Does enrolling via zero-touch slow down or cause any delay to the setup process while it’s retrieving the zero-touch config?
- What happens if my Android Enterprise bind account is disabled or deleted?
- What is the AMAPI MCP server?
- Can I manage Private DNS settings through AMAPI?
- What deployment scenario will a zero-touch device enrol under?
- Why does zero-touch require so much touching?
- Can I set Device Owner without a factory reset?
- Can anyone add a device to the zero-touch console?
- Is it possible for an organisation to add previously-purchased devices to zero-touch?
- Can a MADA device be converted to EDLA?
- Can anyone remove a device from the zero-touch console?
- Does Samsung support zero-touch?
- Is it possible to set a zero-touch default configuration?
- Is it possible to bulk update zero-touch devices?
- Is it possible to change zero-touch resellers?
- Are all zero-touch devices Android Enterprise Recommended?
- What are DPC extras?
- What should I put in DPC extras?
- How do I set up zero-touch enrollment when my device reseller is not a zero-touch partner?
- What happens if a device is uploaded to zero-touch with the wrong manufacturer?
- The device registered with zero-touch, but doesn’t launch during setup, why?
- Does Android Go support zero-touch?
- Why are my zero-touch devices randomly factory resetting?
- Are employee-owned devices eligible for zero-touch?
- How do I turn off Google Play app collections?
- What’s the recommended way of managing private (in-house) applications?
- Is it possible to deploy app shortcuts to the homescreen of an Android Enterprise device?
- What are AMAPI application roles?
- Is it possible to backup & restore device data on a fully managed device?
- What is Lost Mode on Android Enterprise?
- The Google Play iFrame is missing a feature in my UEM. How do I enable it?
- How do I configure allowlist/blocklist domains for Google Chrome?
- Does Picture-in-Picture work in kiosk (lock task) mode?
- How to configure Chrome managed bookmarks
- Why does Samsung Smart Switch not work on fully managed devices?
- Play Protect blocked my DPC, why?
- Can Google Play Protect remove apps from managed devices without admin approval?
- What is enhanced fraud protection, and can it block enterprise apps?
- Has Play Protect changed how it handles sideloaded apps on managed devices?
- What is Google Play developer verification, and how does it affect enterprise?
- Does AMAPI support direct APK installation?
- Why can't I find apps in managed Google Play after approving them?
- Are Google Play System Updates managed by Android Enterprise system update policies?
- What enterprise features are new in Android 15?
- Can I purchase paid apps through managed Google Play?
- Can I control default applications through AMAPI?
- Why is my kiosk app UI broken after updating to Android 15?
- Why are managed Google Play apps stuck on pending?
- Why is work profile enrolment failing?
- Why don't managed configurations work with app tracks?
- How do I prevent users from escaping kiosk (lock task) mode?
- How do I manage credential providers and passkeys on managed devices?
- How does conditional access work with Android Enterprise?
- How does cross-profile data sharing work in a work profile?
- What are the AMAPI device quota limits?
- What is the key attestation root certificate change in 2026?
- Can I rename my managed Google Play organisation?
- How do I manage generative AI apps and features on managed devices?