Contents
Docs
General
- Introduction
- Android versions matrix
- What is Android Enterprise?
- Android Enterprise feature requests
- Considerations when migrating from device administrator to Android Enterprise
- Upgrading your Android Enterprise binding to a managed Google domain
- What is Android Enterprise Recommended?
- Android Enterprise FAQ
- How to migrate Android devices from one EMM to another
- Android Enterprise device testing
- What is Private Space in Android 15, and how can organisations manage it?
- Why don't all Android devices come with GMS?
- What is Android One?
- What are managed configurations?
- Android Enterprise vs Device Admin: Why DA is no longer suitable
- Considerations for choosing Android in the Enterprise
- Feature spotlight: Android Smartlock
- Android glossary
- Android version evolution graphics
- Infobyte: Device Admin deprecation
- How to submit a device for Android Enterprise Recommended validation
- How to view software version information
- How to capture a bug report and device logs
- Gartner comparison of security controls for mobile devices 2019
Provisioning
- How to become a zero-touch enrolment reseller
- Android Enterprise provisioning methods
- What is Android zero-touch enrolment?
- Android Enterprise zero-touch console administration guide
- Android Enterprise DPC identifier collection
- Android Enterprise provisioning guides
- Android Enterprise zero-touch DPC extras collection
- Infobyte: Android Enterprise deployment scenarios
- Infobyte: Android Enterprise fully managed provisioning methods
- Manual Android Enterprise work-managed QR code generation for MobileIron
Work profile
Fully managed
App management
- Set up Hypergate's Kerberos Authentication on MobileIron Core for Android Enterprise
- Managed Google Play, allowlist or blocklist?
- Considerations when deploying MTD with Android Enterprise
- Why you shouldn't install apps from unknown sources
- What is OEMConfig?
- Create and manage private apps for Android Enterprise
- Create and manage web apps for Android Enterprise
- Using Google Play application tracks with EMM
- How to locate a private Android app assigned to an organisation ID
- How to host enterprise apps outside of Google Play
- The Google Play iFrame app approval flow is deprecated
- Android 13 adds notifications access as a runtime permission
- Android 13 & up restricts permissions when apps are sideloaded
- Android 14 blocks apps targeting old Android versions
- Android minimum target SDK matrix
- Android system app database
- How to resolve common Android app install failures, by error message
FAQ
- Is Android Enterprise supported on uncertified (non-GMS) devices?
- Can apps be sideloaded into the Private Space?
- Is Private Space supported on fully managed devices?
- Why don't Private Space apps go through VPN?
- How can apps be managed in the Private Space?
- Are Private Space apps visible to enterprise admins?
- Are Private Space applications truly hidden?
- Does Samsung support Android Enterprise?
- Is it possible to manage personal applications on a work profile device?
- Why has USB data access been disabled suddenly?
- What versions of Android support Android Enterprise?
- How to check if an Android device is GMS/Play Protect certified?
- Is it possible to manage eSIM?
- Can I manage APNs through AMAPI?
- Why is my organisation name showing on managed devices?
- Can I route specific apps through 5G network slicing?
- To use Android Enterprise do I need to buy Google Workspace (G Suite) and register my domain?
- What is a managed Google domain, and should I upgrade?
- Is Android Enterprise supported on XR headsets?
- What devices should I buy for my organisation?
- What is the difference between GMS and EDLA certification for enterprise?
- How do Samsung Knox and Android Enterprise policies interact?
- If Android Enterprise is supported from Lollipop, why is Marshmallow often mentioned instead?
- What’s the difference between Device Admin and Android Enterprise?
- What is the Android Enterprise bind?
- Can I change the account I used to bind Android Enterprise?
- Is it possible to bind Android Enterprise with multiple EMMs using one account?
- How do I remove the Android Enterprise bind from my current EMM?
- How do I choose an EMM for Android Enterprise?
- What network requirements does Android Enterprise have?
- What is Android Enterprise Recommended?
- My AER device doesn’t work properly with Android Enterprise, what should I do?
- What is Advanced Protection, and can it be managed?
- Is Android One better than AER? (Or the other way around?)
- How do I configure Google Workspace domains for provisioning?
- What’s the best provisioning method?
- What’s the difference between allow adding accounts vs allow configure credentials?
- Is it possible to utilise a single VPN connection across the entire device?
- Is it possible to utilise multiple VPN connections within a profile?
- Does Android support Kerberos natively?
- What’s the difference between device based accounts and user based accounts?
- How do I manage the new notifications runtime permission in Android 13?
- Can organisations see applications outside of the work profile?
- What can my employer see on my personal device with a work profile?
- What happens to my data when the work profile is removed?
- What is the difference between MAM and work profiles for BYOD?
- Can organisations deploy applications to the parent profile in a work profile deployment?
- Why does the work profile drain my battery?
- Why are my work profile notifications delayed or missing?
- Is it possible to migrate from DA to AE work profile without a re-enrol?
- Can I turn off my work profile?
- What is a work challenge?
- Enrolment failed but the work profile was created. How do I remove it?
- Why can’t I install or uninstall apps on my managed device?
- How can I provision a fully managed device?
- Is it possible to “retire” (or enterprise wipe) a fully managed device?
- Devices factory reset as soon as they’re enrolled, why?
- Is Factory Reset Protection enabled on fully managed devices?
- What is the difference between FRP and Enterprise FRP?
- Is it possible to migrate fully managed devices between EMM solutions?
- How has COPE changed in Android 11?
- Does Intune support COPE?
- Can organisations see applications outside of the work profile on a COPE device?
- Does Android Enterprise support WearOS?
- Can organisations deploy applications to the parent profile in a COPE deployment?
- Is it possible to migrate from fully managed to COPE without a factory reset?
- How should system applications be handled on a COPE device?
- What OEMs currently support zero-touch?
- Where are zero-touch resellers located?
- Does zero-touch cost anything?
- Does Android Auto work on fully managed devices?
- Is an EMM still required with zero-touch?
- What is the content protection policy in AMAPI?
- What happens if a fully set up device is added to the zero-touch console?
- What happens if a user starts setting up a device before the zero-touch config is applied?
- What happens if a zero-touch config is removed from an enrolled device?
- My AMAPI project returns a usage limit error, why?
- Can I add/remove users on a fully managed device?
- What happens if a new config for a different EMM or server is applied to an enrolled device?
- How can I access a Wi-Fi captive portal when devices are in Kiosk?
- What happens if a zero-touch assigned device is reset?
- What is Device Trust from Android Enterprise?
- Why does zero-touch or KME not trigger after a factory reset on Android 15+?
- What happens if a device is unregistered from the zero-touch console?
- What enterprise features are new in Android 16?
- What is Identity Check on Android?
- Can a device be OTA managed from the zero-touch console?
- What happens when a managed device receives a major Android update?
- Can I migrate devices from a custom DPC to AMAPI?
- Avoiding configuration issues in Google Workspace with GEM & 3rd party EMM
- What is the difference between AMAPI and a custom DPC?
- Does enrolling via zero-touch slow down or cause any delay to the setup process while it’s retrieving the zero-touch config?
- What happens if my Android Enterprise bind account is disabled or deleted?
- What is the AMAPI MCP server?
- Can I manage Private DNS settings through AMAPI?
- What deployment scenario will a zero-touch device enrol under?
- Why does zero-touch require so much touching?
- Can I set Device Owner without a factory reset?
- Can anyone add a device to the zero-touch console?
- Is it possible for an organisation to add previously-purchased devices to zero-touch?
- Can a MADA device be converted to EDLA?
- Can anyone remove a device from the zero-touch console?
- Does Samsung support zero-touch?
- Is it possible to set a zero-touch default configuration?
- Is it possible to bulk update zero-touch devices?
- Is it possible to change zero-touch resellers?
- Are all zero-touch devices Android Enterprise Recommended?
- What are DPC extras?
- What should I put in DPC extras?
- How do I set up zero-touch enrollment when my device reseller is not a zero-touch partner?
- What happens if a device is uploaded to zero-touch with the wrong manufacturer?
- The device registered with zero-touch, but doesn’t launch during setup, why?
- Does Android Go support zero-touch?
- Why are my zero-touch devices randomly factory resetting?
- Are employee-owned devices eligible for zero-touch?
- How do I turn off Google Play app collections?
- What’s the recommended way of managing private (in-house) applications?
- Is it possible to deploy app shortcuts to the homescreen of an Android Enterprise device?
- What are AMAPI application roles?
- Is it possible to backup & restore device data on a fully managed device?
- What is Lost Mode on Android Enterprise?
- The Google Play iFrame is missing a feature in my UEM. How do I enable it?
- How do I configure allowlist/blocklist domains for Google Chrome?
- Does Picture-in-Picture work in kiosk (lock task) mode?
- How to configure Chrome managed bookmarks
- Why does Samsung Smart Switch not work on fully managed devices?
- Play Protect blocked my DPC, why?
- Can Google Play Protect remove apps from managed devices without admin approval?
- What is enhanced fraud protection, and can it block enterprise apps?
- Has Play Protect changed how it handles sideloaded apps on managed devices?
- What is Google Play developer verification, and how does it affect enterprise?
- Does AMAPI support direct APK installation?
- Why can't I find apps in managed Google Play after approving them?
- Are Google Play System Updates managed by Android Enterprise system update policies?
- What enterprise features are new in Android 15?
- Can I purchase paid apps through managed Google Play?
- Can I control default applications through AMAPI?
- Why is my kiosk app UI broken after updating to Android 15?
- Why are managed Google Play apps stuck on pending?
- Why is work profile enrolment failing?
- Why don't managed configurations work with app tracks?
- How do I prevent users from escaping kiosk (lock task) mode?
- How do I manage credential providers and passkeys on managed devices?
- How does conditional access work with Android Enterprise?
- How does cross-profile data sharing work in a work profile?
- What are the AMAPI device quota limits?
- What is the key attestation root certificate change in 2026?
- Can I rename my managed Google Play organisation?
- How do I manage generative AI apps and features on managed devices?
Feature spotlight: Android Smartlock
Contents
A very common question I am asked, almost on every Android deployment I undertake in fact, is “what is Smartlock?”.
It is a commonly overlooked configuration within EMMs, due either to the fact organisations don’t know what it is, or that “smart” in the name gives the wrong impression and is therefore deemed safe.
A quick overview
#Smartlock is a convenience feature in Android that aims to reduce how often a device with a passcode enabled needs to be unlocked in situations where it could be deemed low risk. Some of these situations include:
- Trusted places
- Trusted accessories
- On-body detection
Used correctly it can indeed offer a balance between security and convenience in genuinely trusted environments, however although it can be controlled granularly via some UEM solutions in terms of the types of Smartlock available, it is still frequently subject to overuse or abuse.
Trusted places
#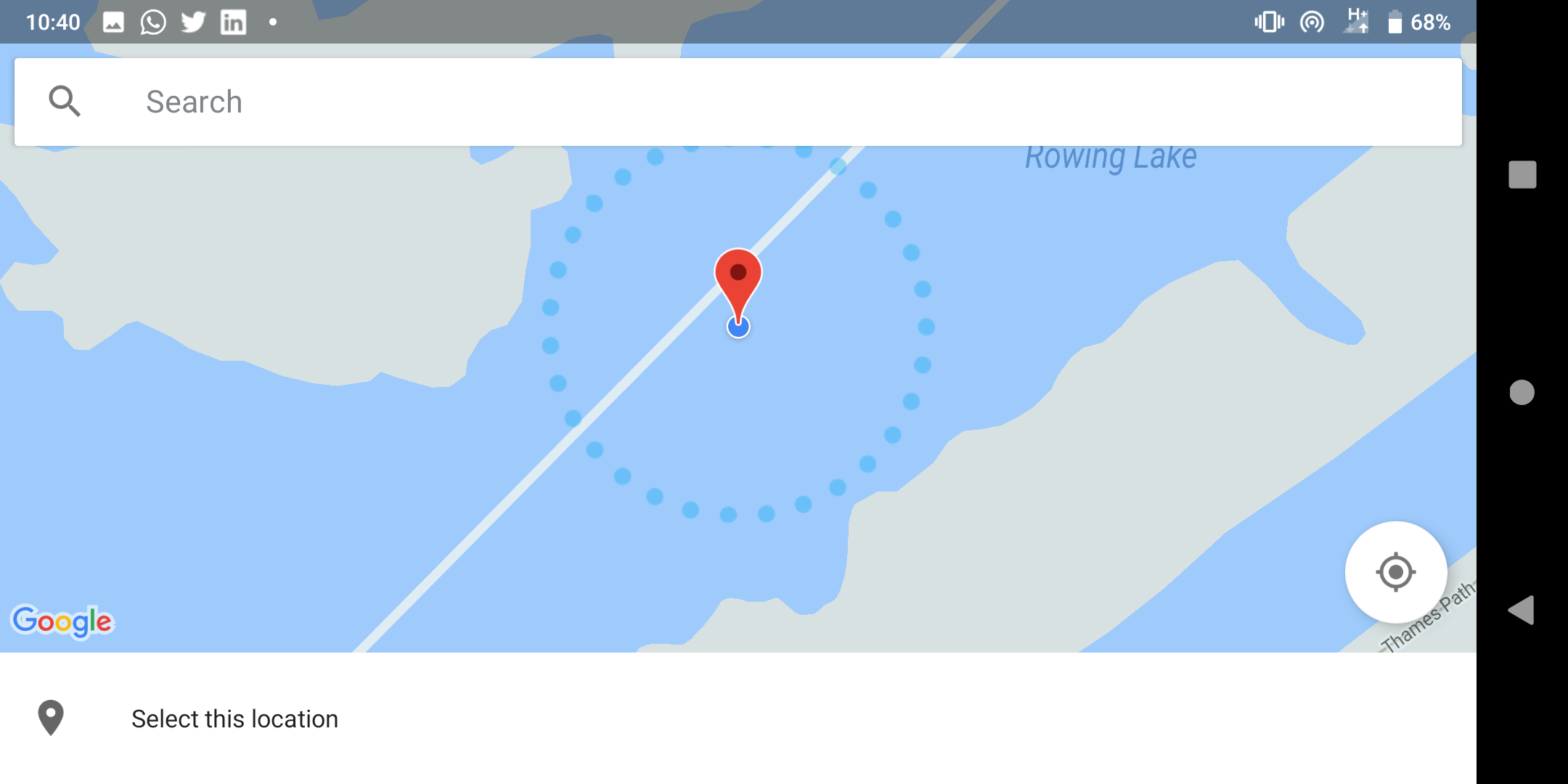 Selecting a trusted location on a map
Selecting a trusted location on a map
If you’re at home, at your parents or a close friend’s home, you’re in a location you trust. It’s unlikely (though not impossible) an unknown bad actor is going to walk into the living room and steal your phone.
It’s fair to assume with the environment considered safe, trusted, you might not need to make use of authentication to gain access to your device.
Herein lies the problem. End-users may select the coffee shop, the local library or the pub as locations where they frequent and don’t want to have their devices lock up.
It is up to the end-user to deem what scenarios are safe; any location in the world, plus a fixed radius around it, can be set as trusted. Not good.
When a device is not locked, it can be stolen and very easily accessed if it’s in a trusted location and this is therefore not a great idea for corporate devices.
Trusted accessories
#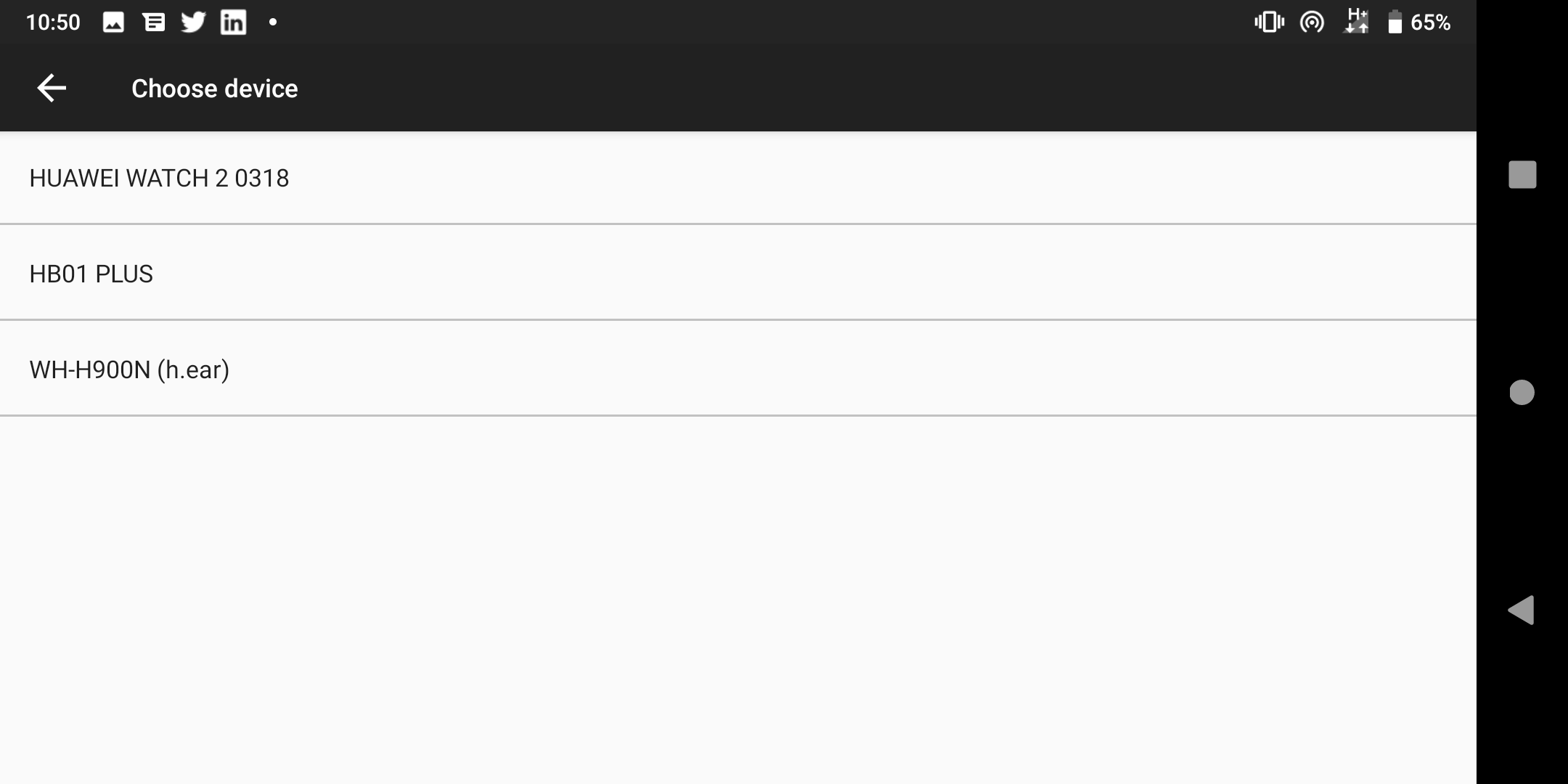 Selecting a trusted device from paired Bluetooth devices
Selecting a trusted device from paired Bluetooth devices
When entering a car, your device might automatically connect up to your Bluetooth system. When out for and about perhaps you have wireless headphones or at home connect up a keyboard and mouse wirelessly for typing up reports.
Trusted accessories allows you to reduce the frequency of inputting the passcode when a device is paired to particular Bluetooth devices.
Once again, since any Bluetooth accessory can be deemed trusted under any circumstance, if the device is stolen and unlocked within range of the Bluetooth accessory, the attacker will have full access to the device; in the case of an item such as a WearOS watch, it could remain unlocked for extended periods of time.
On-body detection
#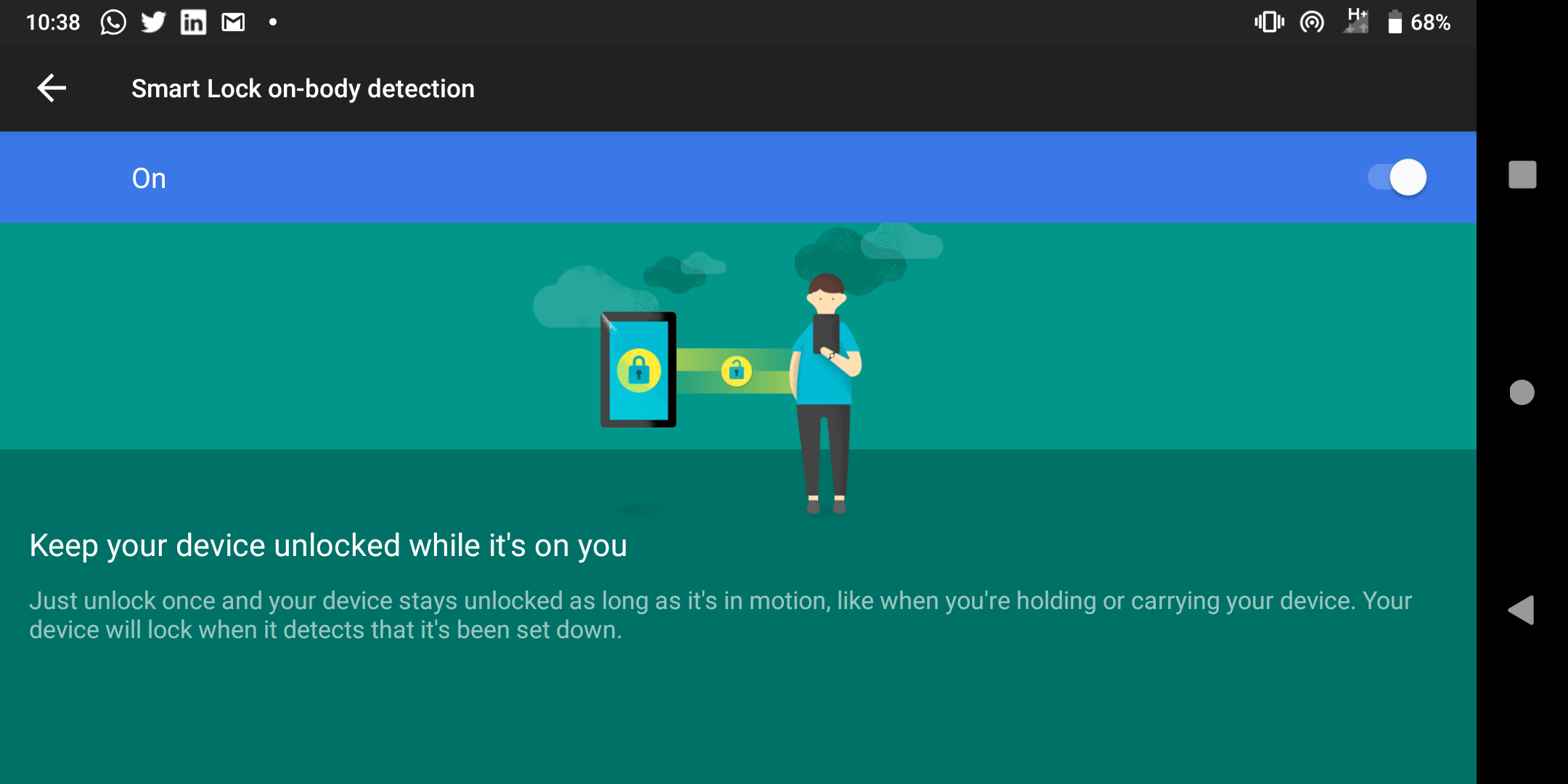 Enabling on-body detection
Enabling on-body detection
An Android device is exceptionally smart. It knows when it’s static, when it’s picked up and even when it’s in motion. Using the latter, if your device detects you moving, it can make the assumption it is on your person and therefore safe.
With on-body detection, as long as the device feels a movement that isn’t dissimilar to the typical bumps, jumps and shakes any device would feel in someone’s pocket or bag, it can remain unlocked.
The very obvious drawback is simply if a device is snatched out of a hand or bag while the end-user is in motion. Whilst the attacker remains in motion, the device remains unlocked, easily accessed for a decent amount of time after the fact.
Why Smartlock is not a great idea
#With the above situations, it is clear Smartlock can be easily taken advantage of by an attacker. For a business device, this risk is absolutely not worth taking for any devices, not least those known to hold sensitive data.
It is with that in mind that Smartlock should therefore be disabled as a matter of course for managed devices. The convenience does not outweigh the very real security risk of leaving it enabled.
Smartlock can be disabled across all modern UEM solutions either in part (on an individual basis) or entirely:
Disabling Smartlock for Workspace One UEM
#Referred to as Keyguard Trust Agent State
Disabling Smartlock for MobileIron Core
#
Disabling Smartlock for Maas360
#Again referred to as Allow Trust agents. Do take note of where this setting is as by default the policy opens within Android Settings and not Android Enterprise Settings.
Conclusion
#If your organisation allows the use of Smartlock today, consider turning it off sooner rather than later. It is a common feature popular among Android users so do expect to justify its disablement, however hopefully the above will provide the necessary information for organisations to do just that.
Docs
General
- Introduction
- Android versions matrix
- What is Android Enterprise?
- Android Enterprise feature requests
- Considerations when migrating from device administrator to Android Enterprise
- Upgrading your Android Enterprise binding to a managed Google domain
- What is Android Enterprise Recommended?
- Android Enterprise FAQ
- How to migrate Android devices from one EMM to another
- Android Enterprise device testing
- What is Private Space in Android 15, and how can organisations manage it?
- Why don't all Android devices come with GMS?
- What is Android One?
- What are managed configurations?
- Android Enterprise vs Device Admin: Why DA is no longer suitable
- Considerations for choosing Android in the Enterprise
- Feature spotlight: Android Smartlock
- Android glossary
- Android version evolution graphics
- Infobyte: Device Admin deprecation
- How to submit a device for Android Enterprise Recommended validation
- How to view software version information
- How to capture a bug report and device logs
- Gartner comparison of security controls for mobile devices 2019
Provisioning
- How to become a zero-touch enrolment reseller
- Android Enterprise provisioning methods
- What is Android zero-touch enrolment?
- Android Enterprise zero-touch console administration guide
- Android Enterprise DPC identifier collection
- Android Enterprise provisioning guides
- Android Enterprise zero-touch DPC extras collection
- Infobyte: Android Enterprise deployment scenarios
- Infobyte: Android Enterprise fully managed provisioning methods
- Manual Android Enterprise work-managed QR code generation for MobileIron
Work profile
Fully managed
App management
- Set up Hypergate's Kerberos Authentication on MobileIron Core for Android Enterprise
- Managed Google Play, allowlist or blocklist?
- Considerations when deploying MTD with Android Enterprise
- Why you shouldn't install apps from unknown sources
- What is OEMConfig?
- Create and manage private apps for Android Enterprise
- Create and manage web apps for Android Enterprise
- Using Google Play application tracks with EMM
- How to locate a private Android app assigned to an organisation ID
- How to host enterprise apps outside of Google Play
- The Google Play iFrame app approval flow is deprecated
- Android 13 adds notifications access as a runtime permission
- Android 13 & up restricts permissions when apps are sideloaded
- Android 14 blocks apps targeting old Android versions
- Android minimum target SDK matrix
- Android system app database
- How to resolve common Android app install failures, by error message
FAQ
- Is Android Enterprise supported on uncertified (non-GMS) devices?
- Can apps be sideloaded into the Private Space?
- Is Private Space supported on fully managed devices?
- Why don't Private Space apps go through VPN?
- How can apps be managed in the Private Space?
- Are Private Space apps visible to enterprise admins?
- Are Private Space applications truly hidden?
- Does Samsung support Android Enterprise?
- Is it possible to manage personal applications on a work profile device?
- Why has USB data access been disabled suddenly?
- What versions of Android support Android Enterprise?
- How to check if an Android device is GMS/Play Protect certified?
- Is it possible to manage eSIM?
- Can I manage APNs through AMAPI?
- Why is my organisation name showing on managed devices?
- Can I route specific apps through 5G network slicing?
- To use Android Enterprise do I need to buy Google Workspace (G Suite) and register my domain?
- What is a managed Google domain, and should I upgrade?
- Is Android Enterprise supported on XR headsets?
- What devices should I buy for my organisation?
- What is the difference between GMS and EDLA certification for enterprise?
- How do Samsung Knox and Android Enterprise policies interact?
- If Android Enterprise is supported from Lollipop, why is Marshmallow often mentioned instead?
- What’s the difference between Device Admin and Android Enterprise?
- What is the Android Enterprise bind?
- Can I change the account I used to bind Android Enterprise?
- Is it possible to bind Android Enterprise with multiple EMMs using one account?
- How do I remove the Android Enterprise bind from my current EMM?
- How do I choose an EMM for Android Enterprise?
- What network requirements does Android Enterprise have?
- What is Android Enterprise Recommended?
- My AER device doesn’t work properly with Android Enterprise, what should I do?
- What is Advanced Protection, and can it be managed?
- Is Android One better than AER? (Or the other way around?)
- How do I configure Google Workspace domains for provisioning?
- What’s the best provisioning method?
- What’s the difference between allow adding accounts vs allow configure credentials?
- Is it possible to utilise a single VPN connection across the entire device?
- Is it possible to utilise multiple VPN connections within a profile?
- Does Android support Kerberos natively?
- What’s the difference between device based accounts and user based accounts?
- How do I manage the new notifications runtime permission in Android 13?
- Can organisations see applications outside of the work profile?
- What can my employer see on my personal device with a work profile?
- What happens to my data when the work profile is removed?
- What is the difference between MAM and work profiles for BYOD?
- Can organisations deploy applications to the parent profile in a work profile deployment?
- Why does the work profile drain my battery?
- Why are my work profile notifications delayed or missing?
- Is it possible to migrate from DA to AE work profile without a re-enrol?
- Can I turn off my work profile?
- What is a work challenge?
- Enrolment failed but the work profile was created. How do I remove it?
- Why can’t I install or uninstall apps on my managed device?
- How can I provision a fully managed device?
- Is it possible to “retire” (or enterprise wipe) a fully managed device?
- Devices factory reset as soon as they’re enrolled, why?
- Is Factory Reset Protection enabled on fully managed devices?
- What is the difference between FRP and Enterprise FRP?
- Is it possible to migrate fully managed devices between EMM solutions?
- How has COPE changed in Android 11?
- Does Intune support COPE?
- Can organisations see applications outside of the work profile on a COPE device?
- Does Android Enterprise support WearOS?
- Can organisations deploy applications to the parent profile in a COPE deployment?
- Is it possible to migrate from fully managed to COPE without a factory reset?
- How should system applications be handled on a COPE device?
- What OEMs currently support zero-touch?
- Where are zero-touch resellers located?
- Does zero-touch cost anything?
- Does Android Auto work on fully managed devices?
- Is an EMM still required with zero-touch?
- What is the content protection policy in AMAPI?
- What happens if a fully set up device is added to the zero-touch console?
- What happens if a user starts setting up a device before the zero-touch config is applied?
- What happens if a zero-touch config is removed from an enrolled device?
- My AMAPI project returns a usage limit error, why?
- Can I add/remove users on a fully managed device?
- What happens if a new config for a different EMM or server is applied to an enrolled device?
- How can I access a Wi-Fi captive portal when devices are in Kiosk?
- What happens if a zero-touch assigned device is reset?
- What is Device Trust from Android Enterprise?
- Why does zero-touch or KME not trigger after a factory reset on Android 15+?
- What happens if a device is unregistered from the zero-touch console?
- What enterprise features are new in Android 16?
- What is Identity Check on Android?
- Can a device be OTA managed from the zero-touch console?
- What happens when a managed device receives a major Android update?
- Can I migrate devices from a custom DPC to AMAPI?
- Avoiding configuration issues in Google Workspace with GEM & 3rd party EMM
- What is the difference between AMAPI and a custom DPC?
- Does enrolling via zero-touch slow down or cause any delay to the setup process while it’s retrieving the zero-touch config?
- What happens if my Android Enterprise bind account is disabled or deleted?
- What is the AMAPI MCP server?
- Can I manage Private DNS settings through AMAPI?
- What deployment scenario will a zero-touch device enrol under?
- Why does zero-touch require so much touching?
- Can I set Device Owner without a factory reset?
- Can anyone add a device to the zero-touch console?
- Is it possible for an organisation to add previously-purchased devices to zero-touch?
- Can a MADA device be converted to EDLA?
- Can anyone remove a device from the zero-touch console?
- Does Samsung support zero-touch?
- Is it possible to set a zero-touch default configuration?
- Is it possible to bulk update zero-touch devices?
- Is it possible to change zero-touch resellers?
- Are all zero-touch devices Android Enterprise Recommended?
- What are DPC extras?
- What should I put in DPC extras?
- How do I set up zero-touch enrollment when my device reseller is not a zero-touch partner?
- What happens if a device is uploaded to zero-touch with the wrong manufacturer?
- The device registered with zero-touch, but doesn’t launch during setup, why?
- Does Android Go support zero-touch?
- Why are my zero-touch devices randomly factory resetting?
- Are employee-owned devices eligible for zero-touch?
- How do I turn off Google Play app collections?
- What’s the recommended way of managing private (in-house) applications?
- Is it possible to deploy app shortcuts to the homescreen of an Android Enterprise device?
- What are AMAPI application roles?
- Is it possible to backup & restore device data on a fully managed device?
- What is Lost Mode on Android Enterprise?
- The Google Play iFrame is missing a feature in my UEM. How do I enable it?
- How do I configure allowlist/blocklist domains for Google Chrome?
- Does Picture-in-Picture work in kiosk (lock task) mode?
- How to configure Chrome managed bookmarks
- Why does Samsung Smart Switch not work on fully managed devices?
- Play Protect blocked my DPC, why?
- Can Google Play Protect remove apps from managed devices without admin approval?
- What is enhanced fraud protection, and can it block enterprise apps?
- Has Play Protect changed how it handles sideloaded apps on managed devices?
- What is Google Play developer verification, and how does it affect enterprise?
- Does AMAPI support direct APK installation?
- Why can't I find apps in managed Google Play after approving them?
- Are Google Play System Updates managed by Android Enterprise system update policies?
- What enterprise features are new in Android 15?
- Can I purchase paid apps through managed Google Play?
- Can I control default applications through AMAPI?
- Why is my kiosk app UI broken after updating to Android 15?
- Why are managed Google Play apps stuck on pending?
- Why is work profile enrolment failing?
- Why don't managed configurations work with app tracks?
- How do I prevent users from escaping kiosk (lock task) mode?
- How do I manage credential providers and passkeys on managed devices?
- How does conditional access work with Android Enterprise?
- How does cross-profile data sharing work in a work profile?
- What are the AMAPI device quota limits?
- What is the key attestation root certificate change in 2026?
- Can I rename my managed Google Play organisation?
- How do I manage generative AI apps and features on managed devices?